The graphic above shows the data flow for a forensics case*. I amalgamated and simplified the processes of the two forensics teams I’ve worked in, to come up with what I believe is the basic flow of a case for any forensics team. Foreman is a framework to support this process flow. It does not dictate how case notes should be written, how a quality check should be done or how tasks should be allocated. This should be in the procedures and process documents the team have. Instead, Foreman allows for easy case management to help forensics teams perform effectively. I’m going to try and write a paper on this, been a while since I wrote something proper, better go blow the dust off the old LaTeX..
There are 4 different sets of people that make up a case – case managers, investigators, requesters and authorisers. Requesters request forensic work which needs to be authorisered by an authoriser. Once authorisered, a case manager needs to accept the case and will be the main point of contact for the case. An investigator is the person who will carry out the forensic case work.
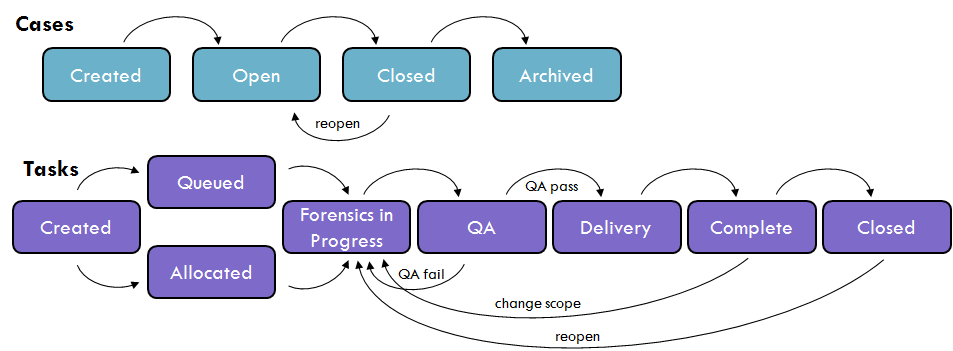
Cases are made up of tasks, which can be divided out to different forensic investigators. For example, there may the task of imaging a device, followed by analysis and a report. A junior member of staff may carry out the image, and a senior member may carry out the analysis & report tasks. Cases can be in one of four states; created, open, closed, archived. A created case is not yet ready to be worked on. This stage would be for the requester and case managers to agree on the tasks and scope of the case. Tasks will generally be added to the case at this point, also in their created stage. Once agreed, the case can be opened.
There are two ways in which an investigator is assigned to a task. You can either allow the investigator to pick tasks themselves from the pool of unallocated tasks, or the case manager can assign tasks to investigators directly. If the investigators are allowed to pick tasks, the case manager will change the task status to queued, otherwise, they will allocate the task and change the status to allocated. Once the investigator has confirmed they are ready to start work on the task, they will change the status to forensics in process. This allows the investigator to update case notes and upload files to Foreman.
The investigator works on the task until it is complete. Some sort of quality assurance (‘QA’) check will take place before the task can be delivered. The nature of the QA will be documented in the forensics process, and it is not for Foreman to dictate how rigorous this should be. Foreman just allows for the investigator to change the status to QA, which will alert the QA partners. QA is normally done by other members of the same team. Foreman allows for a QA pass, which will change the status to delivery, or a QA fail, which would move the task back into forensics in process, where the investigator would redo the mistakes made. The investigator can request QA again by changing the status, and this will go backwards and forwards until a QA pass is gained.
The investigator may need to do some extra work to deliver the data to the requester, such as calculating hash values or updating notes with the delivery location. In the delivery status, the investigator can update the case notes to note this. Once this is complete, the investigator can move the status to complete. At this point the requester has been delivered the work, and they may decide that the original scope of the task was wrong. They may decide to reset the task back to forensics in process, with comments on what they require differently. Otherwise, if they are happy, they can close the task. The task can be reopened at a later date if further work is required.
Once all the tasks for a case are closed, the requester or case manager can close the case. Tasks cannot have their status changed or case notes updated when a case is closed, but if more work is required, the case can be reopened. Finally, when a case is completed and no further work will be required, the case can be archived. All data is preserved in a read only mode.
* – Note that this applies to teams working within a commercial setting, such as in a financial institution. I do not know if this applies more broadly, i.e. with the police, but I have no reason to believe it differs too much. Happy to be challenged!
