It has been 4 years now since Lockheed Martin released their “Cyber Kill Chain” paper, which describes the stages that the perpetrator of an advanced persistent threat (APT) takes. This kind of attack sequencing is not new, the American military and other government forces have used similar models to show the stages of a terrorist attack or how to target enemy missiles:
- The American military use ‘Find, Fix, Track, Target, Engage, and Assess’ to target enemies.
- They also use ‘Board Target Selection, Intelligence Gathering and Surveillance, Specific Target Selection, Pre-attack Surveillance and Planning, Rehearsals, Actions on the Objective, Escape and Exploitation’ for the phases of a terrorist attack.
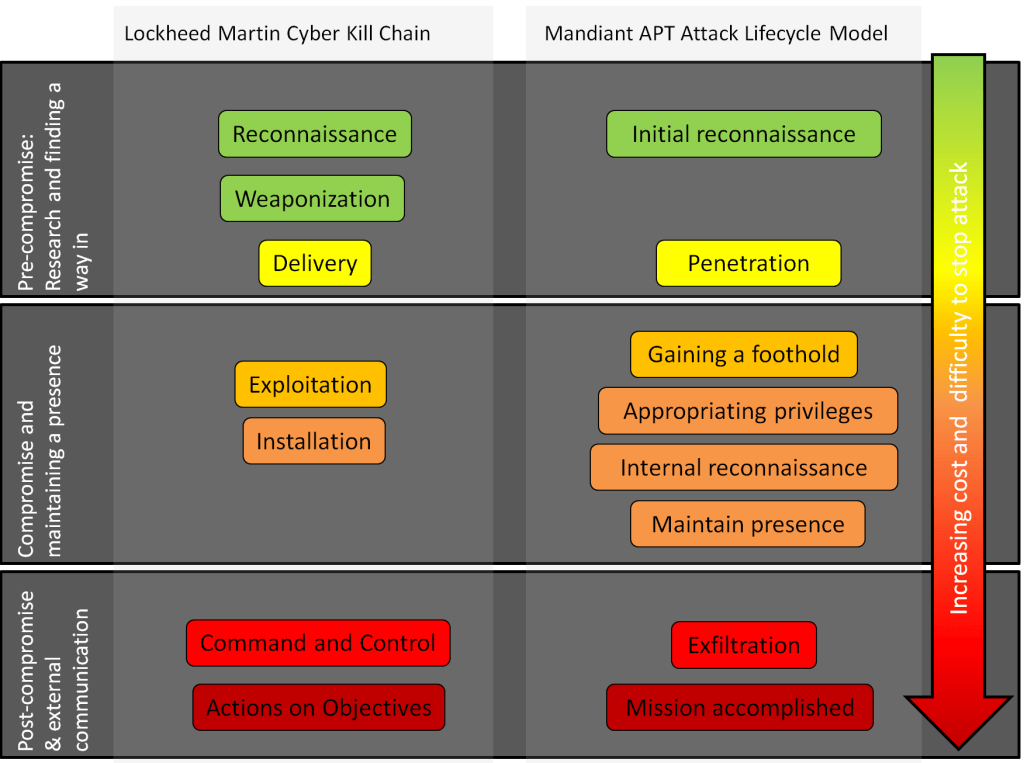
- Lockheed Martin use ‘Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control (C2), Actions on Objectives’ for cyber APT attacks.
- Mandiant use ‘Initial reconnaissance, penetration, gaining a foothold, appropriating privileges, internal reconnaissance, maintain presence, exfiltration, mission accomplished’ for APT and cyber lifecycles.
I have put the Lockheed Martin & Mandiant models in this diagram to show the similarities:
So why are these models so useful for a business looking at its security posture? Well on the surface they breakdown sometimes quite a complex attack into simple, easy to explain stages. Senior management can now understand what an APT attack looks like in the form of a nice diagram.
However really the main advantage is that an attack can be stopped at any point in the chain. This is useful when looking at all the solutions and controls that can be put into place. Adding solutions in different parts of the chain mean there is now defence in layers. Without using such a model, multiple solutions might actually only protect against one part of the chain, which when breached has no other defences. A good analogy that that of a castle. Layers of defence include moats, ramparts, portcullises, multiple walls, towers and murderholes. Without thinking of the different stages a badly designed castle might have one very secure wall (perhaps extra thick and high with holes to drop boiling oil) but nothing else; so once the wall was breached then the whole castle would be breached. As the attacker moves along the chain, it becomes harder (and more expensive) to stop the attack.
At the moment the kill chains, attack sequences, criminal lifecycle or whatever you want to call them, seem to be mainly focused at terrorism and military operations or APT attacks. However I think coming up with a simplified sequence is useful to any business who wants to look at securing their company assets and people. Here is an example using a simplified kill chain for if a company wanted to stop their staff from entering in their bank details to a fake website after getting a phishing email. The controls are just examples of things to think about and I’ve probably left off many different solutions!
Research / Reconnaissance / Target gathering
Attack: the attackers research who to target. Perhaps they use LinkedIn to specifically target certain staff. The attackers also set up fake websites e.g. online banking, ready for people to enter in their details.
Controls: staff education on what information to put on social media and privacy settings. Staff education on spotting phishing emails and what to do. Security team have an awareness of which employees are more vulnerable to phishing due to their position.
Delivery
Attack: the attackers send out the emails to staff.
Controls: implement DMARC or other email authentication. Use anti-spam and phishing software on the email gateways. Set up a mailbox for employees to forward suspicious emails to which get sent to a phishing takedown provider.
Exploit
Attack: the attackers gather the details entered in by users who have clicked on the link in the emails.
Controls: End point machine anti-phishing software, e.g. software that scans all links in emails for known malicious websites and forbids the link to work or redirects the user to a warning page. Block all unknown web pages via a web proxy. Use browser plugins or special browsers that disallow confidential details being entered into websites using blacklists or whitelists.
As you can see, choosing one option from the different parts of the chain would work better than trying to implement everything from one part of the chain. I hope that you can see that having some sort of model of the stages of an attack can be very useful when coming up with security solutions for your company. It doesn’t have to be as complicated at the Lockheed Martin one, but that’s probably a pretty good place to start.
